


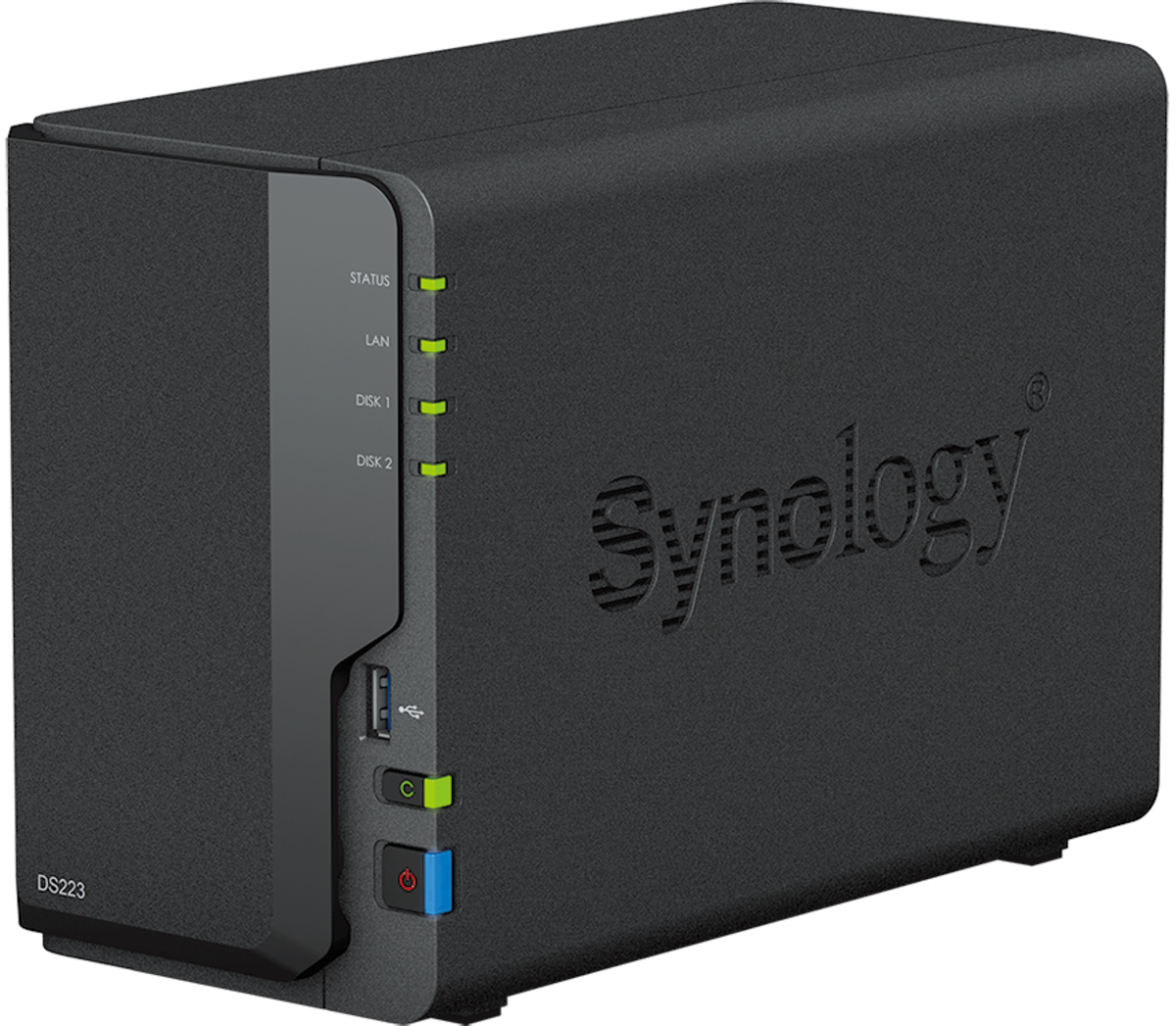



Reliable 2‑bay NAS system for evidence storage, long‑term archiving, and team workflows. Intended for organisations and advanced users handling larger volumes of material.
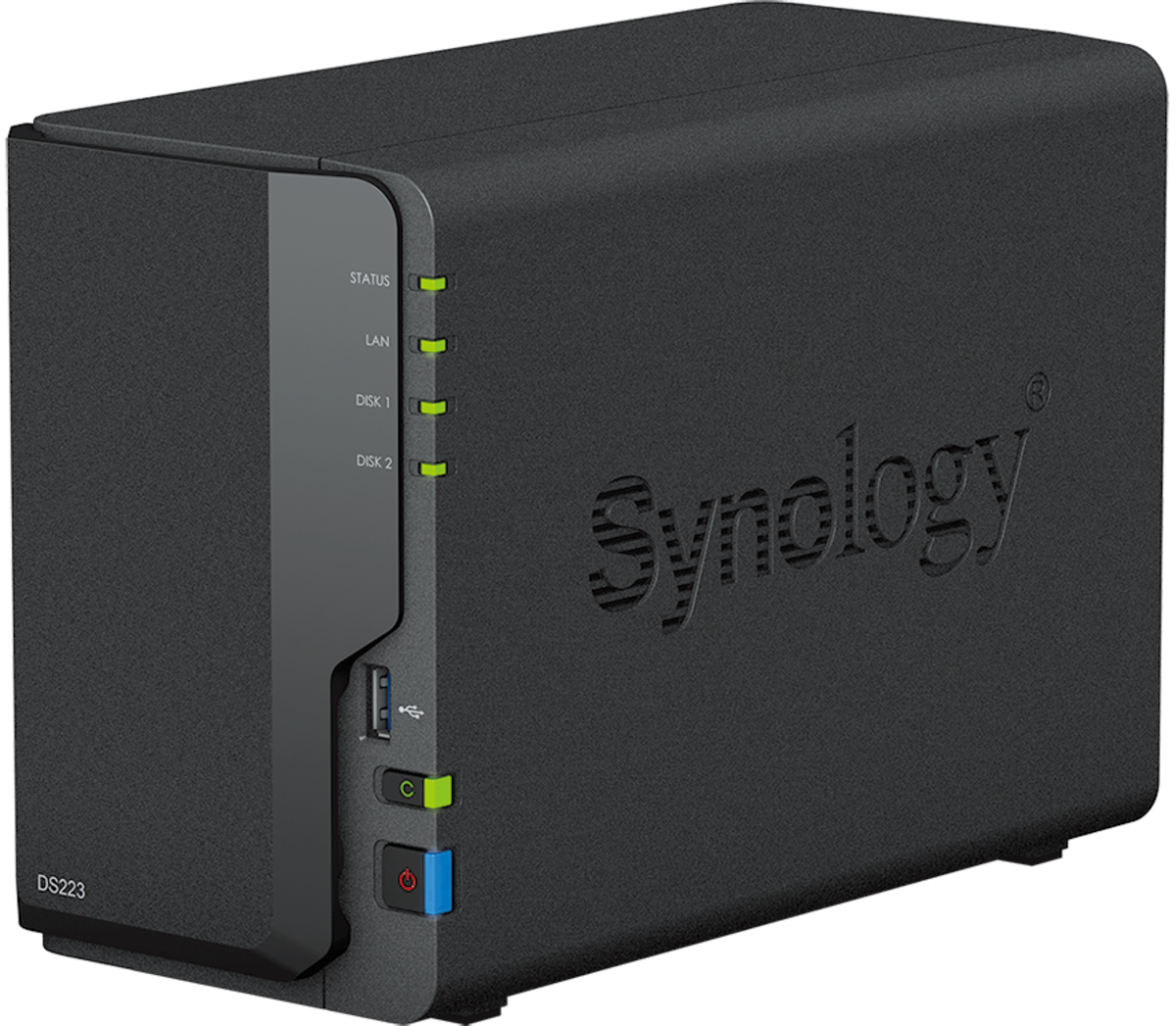
The Synology DS223 is a compact, professional Network‑Attached Storage (NAS) system designed for structured storage, organisation, and controlled access to digital material.
Within an OSINT or investigative context, devices like the DS223 are typically used after collection and analysis, as part of an evidence retention and archiving workflow, rather than during active field work.
This is not an operational device for most volunteers. It is intended for:
If you do not already have a clear need for centralised storage, you likely do not need this device.
(Drives are typically sold separately unless stated otherwise.)
This product is listed as a reference‑grade storage option for advanced users and organisations.
True Observer does not configure, harden, or pre‑load this system by default, and does not provide forensic guarantees.
Correct use requires:
Product Reviews